How Can I Hide My IP Address?

First of all, why would you want to hide your IP address?
In simple terms, hiding (or “masking”) your IP address can reduce the risk of being tracked. An IP address usually does not directly reveal your name, phone number, or other highly sensitive personal details, but it can expose your approximate location (for example, country or city), your ISP or network type, and it may be used by websites to associate and analyze activity coming from the same network.
Common benefits of hiding your IP address include:
- Concealing your rough geographic location (to other sites, your location appears as that of the proxy or VPN server).
- Reducing tracking and behavioral profiling by websites (but this does not mean you are completely anonymous).
- Bypassing IP-based access restrictions or bans (for example, when certain IP ranges have been blacklisted). See also: IP blacklist check.
So, how can you hide your IP address? The most common methods are:
- Proxy server
- Virtual private network (VPN)
- SSH tunnel
Method 1: Use a Proxy Server
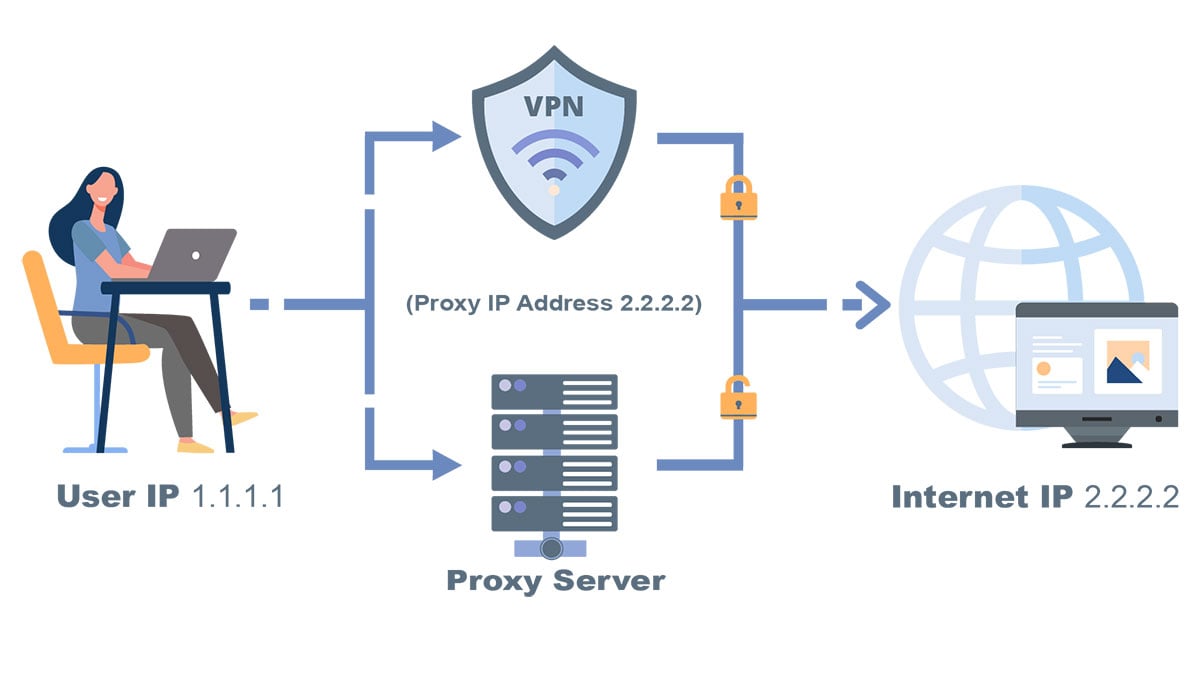
A proxy (proxy server) is a type of network service. Instead of connecting to the target website directly, your device first sends the request to the proxy server. The proxy then forwards the request to the website and returns the response to you. In this setup, the website normally sees the proxy server’s IP address rather than the public IP of your own network.
Key characteristics of using a proxy:
- Advantages: Simple to deploy and convenient for per-site or per-application use (for example, only in your browser). Some proxies allow you to choose the exit country or region.
- Disadvantages: Many free proxies are unstable or slow, and some may log or even tamper with your traffic. If you use an insecure proxy type, your data may be transmitted in plain text.
- Security tips: Prefer reputable providers; use more secure proxy protocols whenever possible, and avoid logging in to important accounts through untrusted free proxies.
How can I get a proxy?
You can search for keywords such as “proxy list”, “SOCKS5 proxy”, or “proxy server” in your search engine. Proxies are usually divided into free and paid services. In general, a reliable paid service is recommended, as stability, speed, and security are easier to control.
Further reading: How to Use a Free Proxy and How to Use a Paid Proxy
Method 2: Use a Virtual Private Network (VPN)
A VPN (Virtual Private Network) creates an encrypted connection (a “tunnel”) between your device and the VPN server. Once the connection is established, websites usually see the VPN server’s IP address as your public IP instead of your original network’s IP. This effectively hides your real IP and changes your apparent exit location.
For example, if you are physically in Hong Kong and connect to a VPN server in the Los Angeles, websites may see a U.S. IP address as your exit IP (based on the VPN provider’s node), rather than your original IP in Hong Kong.
Advantages of using a VPN:
- Broader coverage: A VPN usually applies to the entire device (not just the browser), so it works for most online activities.
- Better security: On public Wi-Fi and similar networks, a VPN can help reduce the risk of eavesdropping or tracking (this still depends on the quality and configuration of the VPN service).
Important notes:
- A VPN does not make you completely anonymous. Your ISP, corporate or school network, and the VPN provider may still be able to link activity to your account.
- Not all websites allow VPN access. Some sites may block VPN traffic or require additional verification.
- Choose a trustworthy provider. Free VPNs or unknown apps may pose privacy and security risks.
How to use a VPN (general steps):
1. Choose a reputable VPN service or set up your own VPN, then install the official client or app on your computer or phone.
2. Open the app and follow the instructions to sign in or import your configuration (details vary by service).
3. Select a server or region (optional), then click “Connect”.
4. After the connection is established, visit any “What Is My IP” page to confirm that your public IP has changed.
5. When you no longer need the VPN, click “Disconnect” to restore your original exit IP.
Best VPN Recommendations:
Method 3: Use an SSH Tunnel
SSH (Secure Shell) is a protocol used for secure remote login and data transfer. It supports encrypted communication. In addition to remote server management, SSH can be used to create a local proxy tunnel (for example, a SOCKS5 proxy) and route your browser traffic through an SSH server. To the outside world, your traffic then appears to come from the SSH server’s IP address.
Note: Using an SSH tunnel as a proxy is an advanced technique and is not very common for everyday users. You usually need your own SSH server and must configure a local SOCKS5 proxy, which is more complex than using a typical VPN.
Typical scenarios where an SSH tunnel is useful:
- You have access to an SSH server (such as a VPS or cloud server).
- You want a relatively lightweight, browser-level proxy solution.
- You are comfortable configuring client settings (this method is more suitable for technical users).
Basic steps:
1. Use SSH on your local machine to create a SOCKS5 proxy listening on a local port (for example, 127.0.0.1:port).
2. In your browser or system proxy settings, configure the SOCKS5 proxy to use that local address and port.
3. After that, websites you visit will see the SSH server’s IP address as your external IP.

How much precision can IP address geolocation reach?
How much precision can IP address geolocation reach?
❓ Question
- Does My IP Address Expose Personal Privacy?
- How Can I Hide My IP Address?
- How Can I Change My IP Address?
- What Is an IP Address?
- What Is the Use of IP Address Lookup?
- Meaning of Information from IP Address Lookup
- What Is the IP Administrator WHOIS Information?
- What Is the Use of IP Administrator WHOIS Information?
- What Is the Meaning of IP Administrator WHOIS Information?
 IP
IP