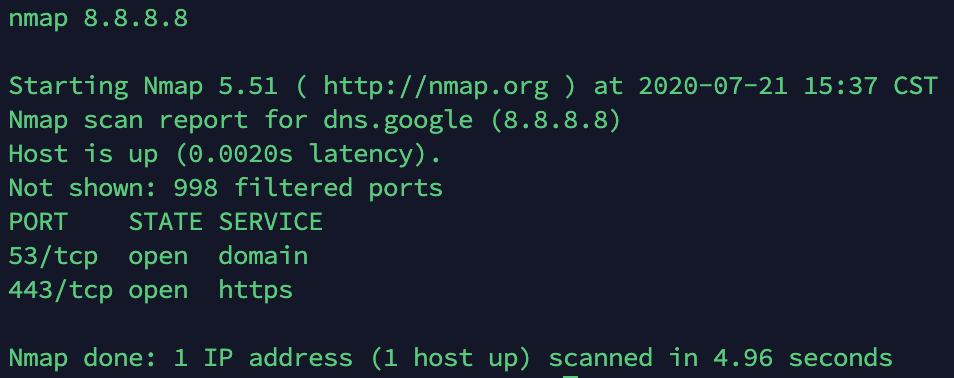
Scan IP Port
Scan Port from Server (172.16.5.201) to IP 52.167.144.176. A port scanner is an application designed to probe a server or host for open ports.
📱 Input
Loading...
Wait 60 seconds after submit.
In computer networking, a port is a communication endpoint. At the software level, within an operating system, a port is a logical construct that identifies a specific process or a type of network service. Ports are identified for each protocol and address combination by 16-bit unsigned numbers, commonly known as the port number. The most common protocols that use port numbers are the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP). Nmap (Network Mapper) is a free and open-source network scanner created by Gordon Lyon (also known by his pseudonym Fyodor Vaskovich). Nmap is used to discover hosts and services on a computer network by sending packets and analyzing the responses.
What is port scanning?
Port scanning is a network reconnaissance technique designed to identify which ports are open on a computer. In addition, port scanners can also identify applications listening on specific ports and the host's operating system and react to traffic in specific ways. For example, HTTP uses port 80, DNS uses port 53, and SSH uses port 22.
What are the port scan results?
Port scan results reveal the state of the network or server. There are three categories that can describe the port scan results: open port, closed port, and filtered port.
Open port: An open port indicates that the target server or network is actively accepting connections or datagrams and has responded to a listening packet. It also indicates that the services used for scanning (usually TCP or UDP) are also in use.
Closed port: A closed port means that the server or network received the request, but there is no service "listening" on that port. A closed port is still accessible and can be used to show that the host is on the IP address. IT administrators should still monitor closed ports as they may change to open and potentially create a vulnerability. They also should be blocked with firewalls, where they become "filtered" ports.
Filtered port: The filtered port indicates that a request packet has been sent, but the host didn't respond or listen. This usually means that the request packet is filtered or blocked by the firewall. If the packet does not reach the destination, the attacker cannot find more information. The filtered port usually responds with an error message like "Unable to access the target" or "No communication".
Wikipedia : Port (computer networking)(en)
In computer networking, a port is a communication endpoint. At the software level, within an operating system, a port is a logical construct that identifies a specific process or a type of network service. A port is identified for each transport protocol and address combination by a 16-bit unsigned number, known as the port number. The most common transport protocols that use port numbers are the Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP).
A port number is always associated with an IP address of a host and the type of transport protocol used for communication. It completes the destination or origination network address of a message. Specific port numbers are reserved to identify specific services so that an arriving packet can be easily forwarded to a running application. For this purpose, port numbers lower than 1024 identify the historically most commonly used services and are called the well-known port numbers. Higher-numbered ports are available for general use by applications and are known as ephemeral ports.
Ports provide a multiplexing service for multiple services or multiple communication sessions at one network address
...🔗 Port (computer networking) ( en )🌐: منفذ (شبكات), Мрежов порт, Síťový port, Ip-port, Port (Protokoll), Puerto de red, درگاه (شبکههای رایانهای), Portti (tietoliikenne), Port (logiciel), פורט (תקשורת), Porta (jaringan komputer), Porta (reti), ポート (コンピュータネットワーク), 포트 (컴퓨터 네트워킹), Port protokołu, Porta (redes de computadores), Port (rețea), Порт (компьютерные сети), Port (datorteknik), Port (ağ), Порт протоколу, 通訊埠,
Wikipedia : Nmap(en)
Nmap (Network Mapper) is a free and open-source network scanner created by Gordon Lyon (also known by his pseudonym Fyodor Vaskovich). Nmap is used to discover hosts and services on a computer network by sending packets and analyzing the responses.
Nmap provides a number of features for probing computer networks, including host discovery and service and operating system detection. These features are extensible by scripts that provide more advanced service detection, vulnerability detection, and other features. Nmap can adapt to network conditions including latency and congestion during a scan.
Nmap started as a Linux utility and was ported to other systems including Windows, macOS, and BSD. It is most popular on Linux, followed by Windows.
Features
Nmap features include:
- Host discovery – Identifying hosts on a network. For example, listing the hosts that respond to TCP and/or ICMP requests or have a particular port open.
- Port scanning – Enumerating the open ports on target hosts.
- Version detection – Interrogating network services on remote devices to determine application
🌐: إن ماب, Nmap, Nmap, Nmap, Nmap, Nmap, انمپ, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap, Nmap,
 IP
IP

